Meeting changing cybersecurity requirements
New Generation Services
Most of the on-line meeting services are now providing links to the new generation of communication services linking two branches of the evolutionary tree: next generation phone and video calls and the growing number of conferencing and meeting services. Together these technologies challenge and will replace the legacy PBX systems and phone networks. This integration is made possible by the use of a common set of standards; Session Initiation Protocol (SIP) for call setup or signalling in telecom parlance and Real-time Transport Protocol (RTP) for audio and video transport (media). An overlapping set of protocols, RTP and Real Time Steaming Protocol (RTSP) are delivering streaming video over the same network infrastructure. Streaming video services bring connectivity to devices such a surveillance cameras and law enforcement/Emergency Services Networks (ESN) bodycam into the ecosystem.
The scope for further integration will drive the evolution of RTC services and will see the emergence of new use cases. One such example is telemedicine. Encouraged by the growing familiarity of video services such as Zoom and WhatsApp, an increasing number of patients are using these services rather than visiting the medical centre in person. Juniper research forecast that the number of health-related teleconsultations is set to reach 765 million worldwide by 2025. (Juniper Research, 2021).
In parallel with these service developments, many national telecommunications providers have plans to switch the provision of phone services for both businesses and consumers from legacy technologies to IP. In many cases these plans are well advanced and new services are being rolled out in advance of the discontinuation of those legacy services. The new networks will provide a further boost to the emergence and adoption of new services.
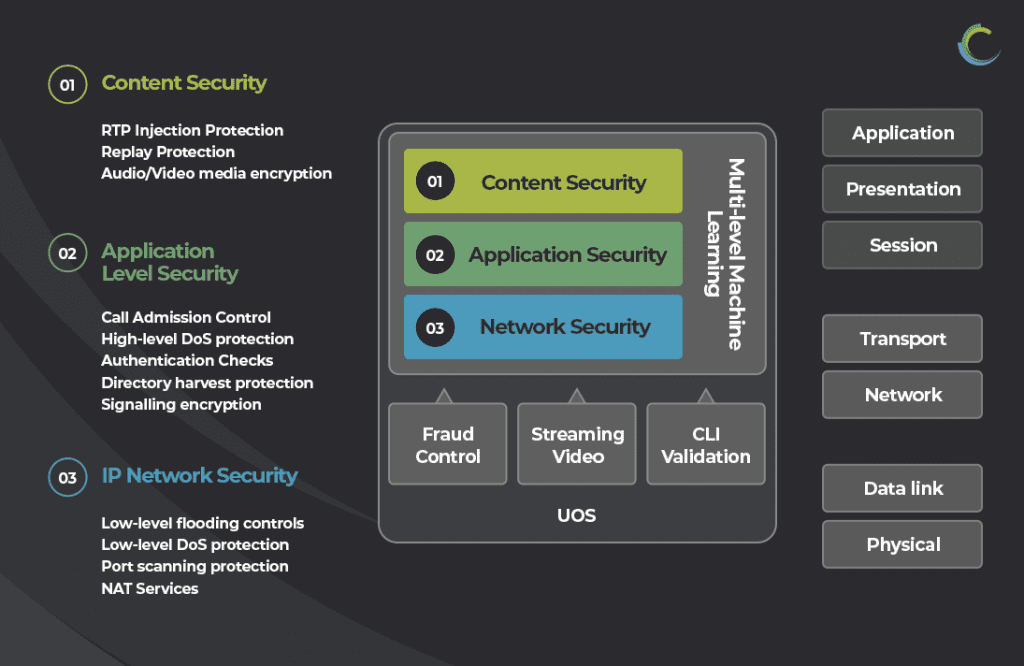
The security risks and vulnerabilities stem from the protocols used to deliver RTC services. These include the standard network level protocols which are shared with other Internet applications and services and a set of protocols unique to RTC services. The RTC protocols have the task of setting up RTC sessions and transporting the audio and video media streams. Two factors add to the complexity of these protocols; the real-time nature of the media streams and the fact that communication services do not follow the same simple client/server model as other services such as email and web. Communications devices can act as both a client (making calls) and a server (receiving calls). When those communications devices are connected to public, untrusted networks, sophisticated security controls are needed. Those controls must protect against threats at multiple levels.